- Use Cases
Regulatory Compliance
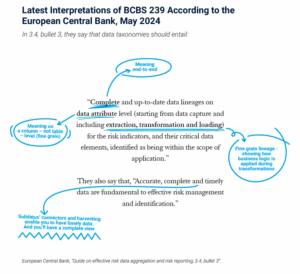
The ECB is “Intensifying its Supervisory Approach” on BCBS239 Compliance – and Basic Lineage is Not Sufficient
Navigate BCBS 239’s rigorous standards with advanced data lineage
Providing Accurate, Complete and Timely Data for BCBS239 Compliance
Discover how to stay ahead in the evolving regulatory landscape of BCBS239
AI
On Demand
Pioneering Data Strategies: How Bank of New York is Shaping Business Success in the Age of AI
Find out about the role of AI and advanced data lineage as AI reshapes the future of business
Unveiling the Path: Why Data Lineage is Crucial for Building Effective AI Products
Read more about data lineage and its business impact, including on AI, BCBS 239 and more
Change Management
Moving to and Within the Cloud
Download this whitepaper for essential advice and guidance on moving to the cloud and succeeding once you’re there. Plus, we discuss regulatory considerations, how to get started, and include a handy pre-migration checklist.
Asset Management Firm Transforms Investment Environment
An asset management firm used Solidatus to carry out a multiyear digital transformation project
Data Governance
NOW: Pensions Achieve Transparency using Solidatus as Central Data Governance Tool
Mapping and modelling a data estate - and showing which data is subject to GDPR
Advanced Data Lineage: A Blueprint for Business Success
Understand the business impact of basic data lineage vs modern, advanced data lineage
Data Products
On Demand
Building Data Trust in LSEG
Hear how Solidatus supports the LSEG Data & Analytics Data Trust Programme
On Demand
Pioneering Data Strategies: How Bank of New York is Shaping Business Success in the Age of AI
Find out about the role of AI and advanced data lineage as AI reshapes the future of business
Decision Making and Reporting
How Data Lineage Helps our Customers Trust the Data Used in Reports and Strategic Decisions
How data lineage supports Solidatus customers with reporting and decision making
Advanced Data Lineage: A Blueprint for Business Success
Understand the business impact of basic data lineage vs modern, advanced data lineage
Operational Resilience
- Product
Data Lineage
Solidatus Chosen as Microsoft Purview’s Data Lineage Integration Partner
Microsoft names Solidatus as key technology partner in their reimagined data governance experience with Microsoft Purview.
Advanced Data Lineage: A Blueprint for Business Success
Understand the business impact of basic data lineage vs modern, advanced data lineage
Integrations and Solutions
Solidatus Chosen as Microsoft Purview’s Data Lineage Integration Partner
Microsoft names Solidatus as key technology partner in their reimagined data governance experience with Microsoft Purview.
Solidatus is a proud participant in the Microsoft Security Store Partner Ecosystem
Solidatus, a leading provider of data lineage solutions, today announced its inclusion in the Microsoft Security Store Partner Ecosystem.
AI Lineage Assistant
On Demand
Pioneering Data Strategies: How Bank of New York is Shaping Business Success in the Age of AI
Find out about the role of AI and advanced data lineage as AI reshapes the future of business
Advanced Data Lineage: A Blueprint for Business Success
Understand the business impact of basic data lineage vs modern, advanced data lineage
Solidatus for Microsoft Purview
Integrations and Solutions
When building or expanding your map view of data flows, you need to capture as much specific information as possible from your systems, such as column structures, data transformations, and more.
AI Lineage Assistant
Ask questions in natural language and the AI drafts data lineage mappings, analyzes impact, and converts unstructured documents into models.
- Resources
- Resources
Past Event
DataVision Americas 2025
Join us in New York City (or virtually) on December 9th to hear from industry experts and practitioners and network with your peers as we explore critical data management and advanced analytics topics. DataVision 2025 is COMPLIMENTARY for members, prospective members, guests and all data management professionals.
Why Truth Beats Hope in Banking
Most AI failures don’t come from the model—they come from the data feeding it.
What is Data Lineage?
Blog
The 48-Hour Test: Does Your AI Have Complete Data Lineage?
Three institutions receive the same question during Model Risk Management reviews: “Walk us through the complete data lineage for your credit decisioning models.
How data lineage prevents AI failures in financial services
Solidatus’ Tina Chace and fellow experts reveal why 90% of AI model failures trace back to upstream data changes
Webinars and Events
On Demand
Zero To Lineage on Demand
Deliver clarity from chaos - at speed. Data lineage is one of the most critical foundations for governance, compliance, and transformation, but getting started can feel like climbing a mountain.
Past Event
DataVision Americas 2025
Join us in New York City (or virtually) on December 9th to hear from industry experts and practitioners and network with your peers as we explore critical data management and advanced analytics topics. DataVision 2025 is COMPLIMENTARY for members, prospective members, guests and all data management professionals.
Case Studies
Royal London Asset Management (RLAM) Builds Operational Data Blueprint
How RLAM used Solidatus to carry out critical digital transformation initiatives
Transforming HSBC’s Lending Business with Solidatus
HSBC's scalable lineage solution is applied to many uses, from ESG to liquidity calculations and more
Whitepapers
Factsheets
Podcasts
The Data Governance Podcast
"Having that complete picture of your data estate is foundational for data governance". In this podcast, Nicola Askham, The Data Governance Coach, speaks with Steve Neat, CRO at Solidatus, about the importance of data lineage for regulatory compliance, AI, and more.
From Months to Minutes: The Benefits of Automated Data Sharing
"Approvals are now sought and gained in minutes, rather than in months". In this podcast, Susan Walsh, Founder and MD of The Classification Guru, speaks with Kate Platonova, Group CDO at HSBC, and Lorraine Waters, CDO at Solidatus, about how HSBC is modernizing data sharing with their DataVisa initiative.
FAQs
- Resources
- Partners
Our Partners
Microsoft Purview Partnership
Understand and truly trust the data at the basis of your business, through a visual map view of its journey from source, through all systems, to destination.
EDM Council
EDM Council members gain more value from these models and can map requirements to their organization’s data fabric. This offers more effective management of your processes, people, data, and technology.
Microsoft Purview Partnership
Our Partners
Solidatus works with a select network of industry-leading partners across Consulting, Technology and Hyperscaler platforms, to enable our customers to deliver impactful, scalable, and sustainable data transformations across their business.
EDM Council
EDM Council members gain more value from these models and can map requirements to their organization’s data fabric. This offers more effective management of your processes, people, data, and technology.
EDM Council
EDM Council
EDM Council members gain more value from these models and can map requirements to their organization’s data fabric. This offers more effective management of your processes, people, data, and technology.
Microsoft Purview Partnership
Understand and truly trust the data at the basis of your business, through a visual map view of its journey from source, through all systems, to destination.
- About Us
- About Us
Careers
Solidatus Announces Strategic Investment from CITI
Solidatus announce a strategic investment from Citi, the leading global bank. Citi is also implementing the Solidatus platform internally, at a global enterprise level.
Alteryx Partnership Helps Demonstrate Connected Governance
Solidatus has enhanced its alliance with Alteryx, helping shared customers visualize data flow across their Alteryx workflows through the Solidatus interface.
Contact
Ready for Vietnam’s New Data Protection Era?
"Vietnam is poised to pass a new decree that will bring the nation into line with its peers across APAC and internationally when it comes to personal data protection."
A-Team Data Management Insight Awards 2021
We are excited to announce that we have been named as the winners of two categories at the A-Team Data Management Insight Awards 2021.
News
How M&T Bank ensures data quality as it implements gen AI
Andrew Foster, the bank's chief data officer, explained how he has been instilling data discipline across the organization and making the bank's data AI-ready.
Tracking data lineage from data archaeology to digital twins
Data management must now grow and evolve a new arm that extends to data lineage control. As data streams flow through IoT machines, users, applications The ability to map and manage living data systems could be set to become an essential part of how enterprises build resilience and maintain trust.
- What is Data Lineage?
- Request a Demo
Anti-Bribery and Corruption Policy
Solidatus is fully committed to the fight against financial crime and makes every effort to remain in full compliance with all applicable financial crime compliance laws, regulations and standards in all of the jurisdictions in which it operates.
Health and Safety Policy
Solidatus takes the health and safety of its employees seriously. Relevant risk assessments are completed and actions arising out of those assessments implemented. We provide clear instructions and information, and adequate training, to ensure employees are competent to do their work.
Information Security Policy
Solidatus takes information security seriously and will at all times ensure that its operations comply with the highest prevailing industry best practices, applicable laws and regulations, and other security requirements.
Modern Slavery and Human Trafficking Policy
Our organization is absolutely committed to preventing slavery and human trafficking in its corporate activities, and to ensuring that its supply chains are free from slavery and human trafficking.
Quality Management Policy
Quality is important to our business because we value our customers. We strive to provide our customers with products and services which meet and even exceed their expectations.
Newsletter
Subscribe for the latest news, blogs, and resources.